Worthless Capture
You're never gonna sniff again
Faulty packets got no meaning
Though it's easy to pretend
I know I'm not a fool
Oh, how I want to sing those lyrics. To whom, you ask? Why, to Cisco Clean Air access points. Also, AirMagnet Enterprise sensors, Aruba Air Monitors and anything else that offers me acareless whisper worthless capture.
Unlike WHAM!, distributed WLAN analysis is in. It seems that nowadays I can't swing a dead cat without hitting someone who is proud as punch of their system of distributed sensors that does something (spectrum analysis, intrusion detection, frame capture) cool.
Distributed sniffing (meaning frame capture) or spectrum analysis does have its uses. If you need to find a rogue AP, identify a denial of service attack or get a general overview of your RF environment, systems like Cisco CleanAir, Fluke AirMagnet Enterprise and Aruba AirWave RAPIDS can all be useful. The problem is that these products are often used for more than that.
Any distributed sniffing product relies on the fundamental conceit that the capture is accurate. If a distributed capture AP/sensor sees a station transmitting 70% of its frames at a 52 Mbps rate, then the sniffing software assumed that, indeed, 70% of that station's frames went through the air at 52 Mbps. The problem is that a distributed sensor is not at the same location as the station. Once a capture is done away from the location of a station, the capture becomes nearly worthless. Too many things about the RF environment will be different for the information to have any value.
The differences between captures near a station and far away from a station can be seen below.
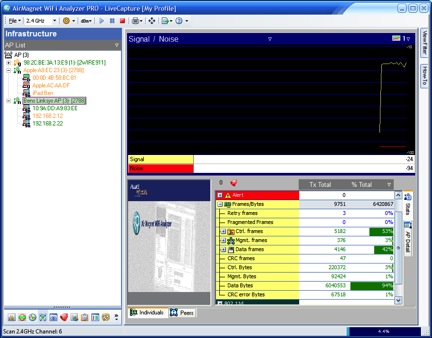
First, a capture done with Fluke AirMagnet WiFi Analyzer filtered only my AP's traffic. The capture device is placed right near my AP as a movie was streaming from an iPad that was about 35 feet away (with some obstructions in between):
The important thing to look at is the CRC Error percentage. When the CRC error percentage is low, that means that the capture is useful. Here the CRC error percentage is 0%, so this is a good capture. And that is usually the case when AP/sensors capture frames being transmitted by other APs. Both devices are typically mounted in the same general space as each other, so very few frames are missed.
The problem shows up when I look at the same AirMagnet capture filtered on my iPad. The capture device is in the same place it was before (near the AP), but the iPad is about 35 feet away (with several obstructions in between the AP and iPad):
It's tough to read, but that screenshot shows that a whopping 28% of captured frames being transmitted by my iPad were read as CRC Errors. That is a worthless capture. It may be showing me 30% Retrys (a bad number for just about any WiFi network), but when over one quarter of my frames were corrupted on capture there is no way of knowing it that is the true percentage of collisions.
The real crime in all of this is that AP/sensor-based captures of frames and RF energy are commonly used by controllers and wireless management software to determine important parameters like AP channel and AP transmit power. And wireless intrusion detection systems use these captures to warn you about alarms. Sometimes this information is good enough to help, but often times the result is poor channel selection, AP-on-AP interference and false IDS alarms.
I realize that it is silly to recommend that people do station-located frame captures for every little WiFi problem, but I do think that many organizations ignore the huge differences in quality between AP/sensor captures and portable captures. My advice is to use distributed AP/sensor-based capture products for rogue AP response, DoS detection and location tracking, and use portable sniffing software to identify problems with the more serious wireless problems like channel selection, AP interference, mobility and collisions.
Faulty packets got no meaning
Though it's easy to pretend
I know I'm not a fool
Oh, how I want to sing those lyrics. To whom, you ask? Why, to Cisco Clean Air access points. Also, AirMagnet Enterprise sensors, Aruba Air Monitors and anything else that offers me a
Unlike WHAM!, distributed WLAN analysis is in. It seems that nowadays I can't swing a dead cat without hitting someone who is proud as punch of their system of distributed sensors that does something (spectrum analysis, intrusion detection, frame capture) cool.
Distributed sniffing (meaning frame capture) or spectrum analysis does have its uses. If you need to find a rogue AP, identify a denial of service attack or get a general overview of your RF environment, systems like Cisco CleanAir, Fluke AirMagnet Enterprise and Aruba AirWave RAPIDS can all be useful. The problem is that these products are often used for more than that.
Any distributed sniffing product relies on the fundamental conceit that the capture is accurate. If a distributed capture AP/sensor sees a station transmitting 70% of its frames at a 52 Mbps rate, then the sniffing software assumed that, indeed, 70% of that station's frames went through the air at 52 Mbps. The problem is that a distributed sensor is not at the same location as the station. Once a capture is done away from the location of a station, the capture becomes nearly worthless. Too many things about the RF environment will be different for the information to have any value.
The differences between captures near a station and far away from a station can be seen below.
First, a capture done with Fluke AirMagnet WiFi Analyzer filtered only my AP's traffic. The capture device is placed right near my AP as a movie was streaming from an iPad that was about 35 feet away (with some obstructions in between):
The important thing to look at is the CRC Error percentage. When the CRC error percentage is low, that means that the capture is useful. Here the CRC error percentage is 0%, so this is a good capture. And that is usually the case when AP/sensors capture frames being transmitted by other APs. Both devices are typically mounted in the same general space as each other, so very few frames are missed.
The problem shows up when I look at the same AirMagnet capture filtered on my iPad. The capture device is in the same place it was before (near the AP), but the iPad is about 35 feet away (with several obstructions in between the AP and iPad):
It's tough to read, but that screenshot shows that a whopping 28% of captured frames being transmitted by my iPad were read as CRC Errors. That is a worthless capture. It may be showing me 30% Retrys (a bad number for just about any WiFi network), but when over one quarter of my frames were corrupted on capture there is no way of knowing it that is the true percentage of collisions.
The real crime in all of this is that AP/sensor-based captures of frames and RF energy are commonly used by controllers and wireless management software to determine important parameters like AP channel and AP transmit power. And wireless intrusion detection systems use these captures to warn you about alarms. Sometimes this information is good enough to help, but often times the result is poor channel selection, AP-on-AP interference and false IDS alarms.
I realize that it is silly to recommend that people do station-located frame captures for every little WiFi problem, but I do think that many organizations ignore the huge differences in quality between AP/sensor captures and portable captures. My advice is to use distributed AP/sensor-based capture products for rogue AP response, DoS detection and location tracking, and use portable sniffing software to identify problems with the more serious wireless problems like channel selection, AP interference, mobility and collisions.


6BB878DF92
ReplyDeleteWhatsapp Şov
Telegram Görüntülü Şov
Canlı Show Whatsapp