Sniffing on a Mac (updated)
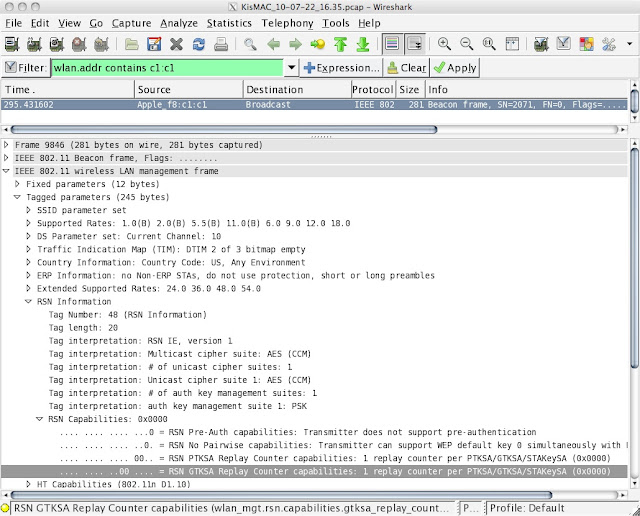
One of my first posts for this blog was a discussion of how Mac OS X users might perform WiFi sniffing. Enterprise-class sniffers only run on Windows, so my earlier post is about using a combination of KisMAC and Wireshark. This brief post is about using WildPackets OmniPeek. Keith Parsons, the WiFi expert who runs WLANpros.com , informed me after my post that I should try running professional grade analyzers using a virtual machine like Parallels or VMWare Fusion. Well, here we are a mere 6 months later and I've finally taken the time to do it. And it works. And it is superb. My basic setup includes the following: MacBook Pro running Mac OS X 10.6.4 (Snow Leopard) with a 2.4 GHz processor and 4 GB of RAM Windows XP Service Pack 3 Parallels Desktop 5 WildPackets OmniPeek Enterprise 6 Linksys WUSB600N 802.11n dual-band USB adapter OmniPeek starts up and runs fine under this setup, though I did wonder if running in a virtual machine would compromise performance. I have